
Member-only story
How to use GCP Secret Manager to Manage your Secrets using Terraform
You are going to start building your first application in GCP (Google Cloud Platform) and the question popup into your mind: How am I going to manage my credentials and secrets?
There are several options, however in this story, we are going to use GCP Secret Manager, so we can securely store and access API keys, passwords, certificates, and other sensitive data from Terraform.
Note: all secrets we will be stored in clear text in the Terraform state file and you need to take security measures to protect it.
1. Prerequisites
This is the list of prerequisites required:
- GCP Subscription: If we don’t have a GCP subscription, we can create a free account at https://cloud.google.com before we start.
- GCP Service Account: is an identity used to authenticate to GCP. Check How to Create a Service Account for Terraform in GCP for instructions to create one.que
- Existing GCP Project: we need an existing GCP project to store our Secret Manager resources.
2. Enabling Secret Manager API (optional)
Before we can use the Secret Manager in our Terraform code, we will need to enable the Secret Manager API in our project. This step is mandatory.
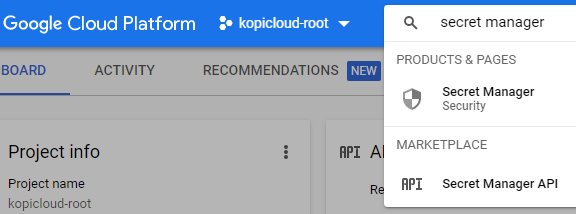
We open the GCP Portal and type secret manager in the search box located at the top of the page.
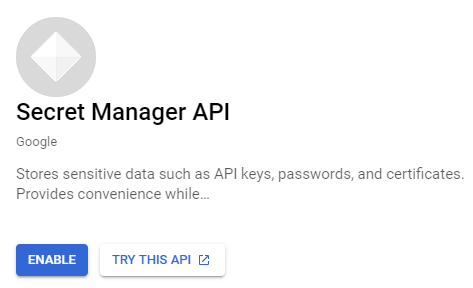
then we click the Enable button.
3. Setting up Service Account Permissions
We need to update our Service Account with extra permissions. We open the GCP Portal and go to IAM & Admin and select IAM.
We select our Service Account and click on the Edit Permissions button (the pencil icon) and we add the following roles:
